Compliance
Why Trust, Security, and Compliance Matter
SMI Aware supports matters where information is scrutinized, challenged, and relied upon in high-stakes decisions. In these environments, how information is collected, documented, and preserved matters as much as what is found.
Our approach is designed to reduce risk for legal teams by aligning disciplined processes, secure infrastructure, and clear documentation with the standards attorneys expect when information may be relied upon in litigation, investigations, or formal review.
Designed for Defensible Authentication
Designed for defensible authentication under the Federal Rules of Evidence.
SMI Aware’s collection and documentation practices are built to support authentication consistent with Federal Rule of Evidence 901(b). Our methods emphasize establishing that information is what it purports to be through clear attribution, documented processes, and reliable preservation.
We do not rely on screenshots, informal searches, or undocumented workflows. Instead, our analysts follow controlled procedures that focus on:
- Clear identification and attribution of content to the correct individual
- Documented collection methods and defined scope
- Preservation of relevant context
- Retention of supporting metadata and source information
- Consistent documentation that allows findings to be explained, reviewed, and evaluated
This approach supports legal teams when questions of authenticity arise, whether during discovery, motion practice, internal review, or later stages of litigation.
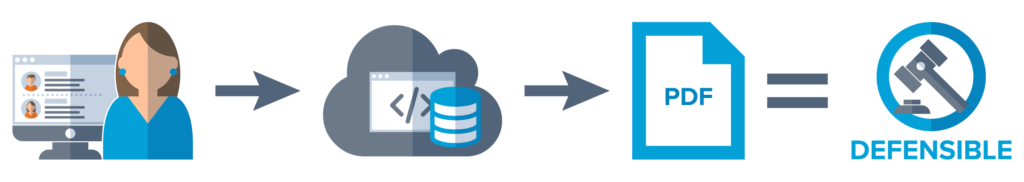
Reports delivered as a PDF serve as an
easy-to-read file that can be shared with your team, while protecting the digital chain of custody.
All of this supports defensible preservation
from social media and the deep web.
Secure Collection and Handling
SMI Aware’s systems and workflows are designed to protect sensitive matters and minimize exposure.
Our controls emphasize:
- Restricted access and role-based permissions
- Secure, matter-based intake and handling
- Disciplined information retention and preservation practices
- Separation between collection, analysis, and reporting functions
These safeguards protect both our clients and our analysts by ensuring information is handled responsibly, consistently, and with appropriate oversight.
Compliance Framework
SMI Aware maintains formal compliance with recognized standards that support secure, defensible operations and evidentiary reliability.
Our compliance posture is designed to align technical controls, process discipline, and documentation practices with how information is evaluated and relied upon in legal matters.
Certifications, Standards, and Evidentiary Alignment
- SOC 2 compliant and certified
- Compliant with ISO 27050 eDiscovery standards
- Collection and documentation practices aligned to support authentication under Federal Rule of Evidence 901(b)
These frameworks and standards reinforce structured access controls, auditability, disciplined handling of information, and documented methods that support defensible authentication when information may be scrutinized in litigation, investigations, or formal review.
Professional Memberships
SMI Aware participates in professional organizations aligned with legal, investigative, and information-governance standards:
- Professional Background Screening Association (PBSA)
- American Society of Trial Consultants (ASTC)
- Legal Tech Hub (LTH)

Compliance as Risk Reduction
Our compliance posture is not designed to satisfy a checklist. It is designed to reduce risk for legal teams.
By combining disciplined process control, secure infrastructure, and documentation aligned with evidentiary expectations, SMI Aware helps clients rely on information with confidence, knowing it was collected, reviewed, and preserved with scrutiny in mind.
